Development of Secured Components & Systems in Emerging Technologies through Hardware & Software Evaluation (DeSCEmT)
Overview
In December 2023, the center was awarded a project entitled “Development of Secured Components & Systems in Emerging Technologies through Hardware & Software Evaluation” (DeSCEmT). The project is funded by the Cyber Security Agency of Singapore (CSA) and National Research Foundation, Singapore (NRF).
In the past decade, mobile devices and Internet of Things (IoT) have become prevalent in our daily lives, both in business and social settings. The applications of such devices have also been growing exponentially due to the development of technologies that support artificial intelligence (AI) and cloud computing. The advances of cloud and mobile computing in the past decade have fundamentally reshaped the computing infrastructure used by individual, business, and government users into a distributed, heterogenous and collaborative system. Modern applications are hence often built as a fusion of data, software, and services from a mixture of stakeholders. Growing with this evolution are the deep-rooted security concerns over a broad spectrum of issues such as leakage of private data, infringement of software copyrights, and corruption of computation results.
This research programme gathers a core team of experts from the Nanyang Technological University (NTU) and the Singapore Management University (SMU) to tackle these security concerns. The SMU team aims to holistically address security challenges in the mobile and cloud computing ecosystem pivoting on the new so-called "confidential computing" techniques featuring hardware-based Trusted Execution Environments (TEEs). The research outcomes are expected to build up the infrastructure and capabilities towards a zero-trust computing domain for industry and government users.

Technical approach
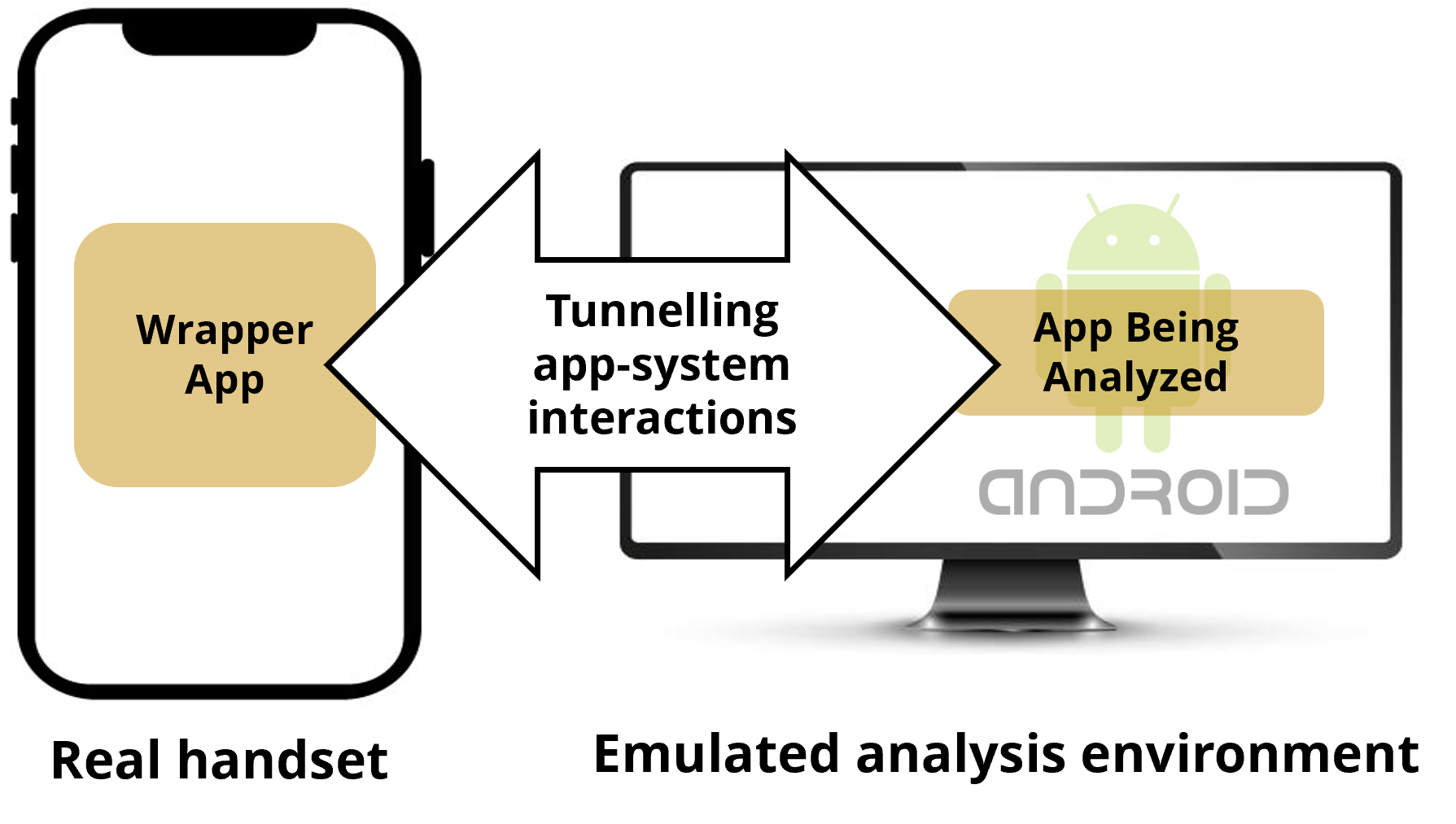
- De-couples the analyzing mechanism from app execution environment
- Runs the analyzing system on powerful emulators
- Uses offloading techniques to mirror app-system interactions to a real handset
Benefits
- Malicious apps can no longer detect the existence of analyzing platform
- Lower performance overhead
- Supports non-pixel phones
Translation opportunities
- Security vetting of mobile apps for government agencies and industry
- Collaborators: DSO, DSTA, GovTech
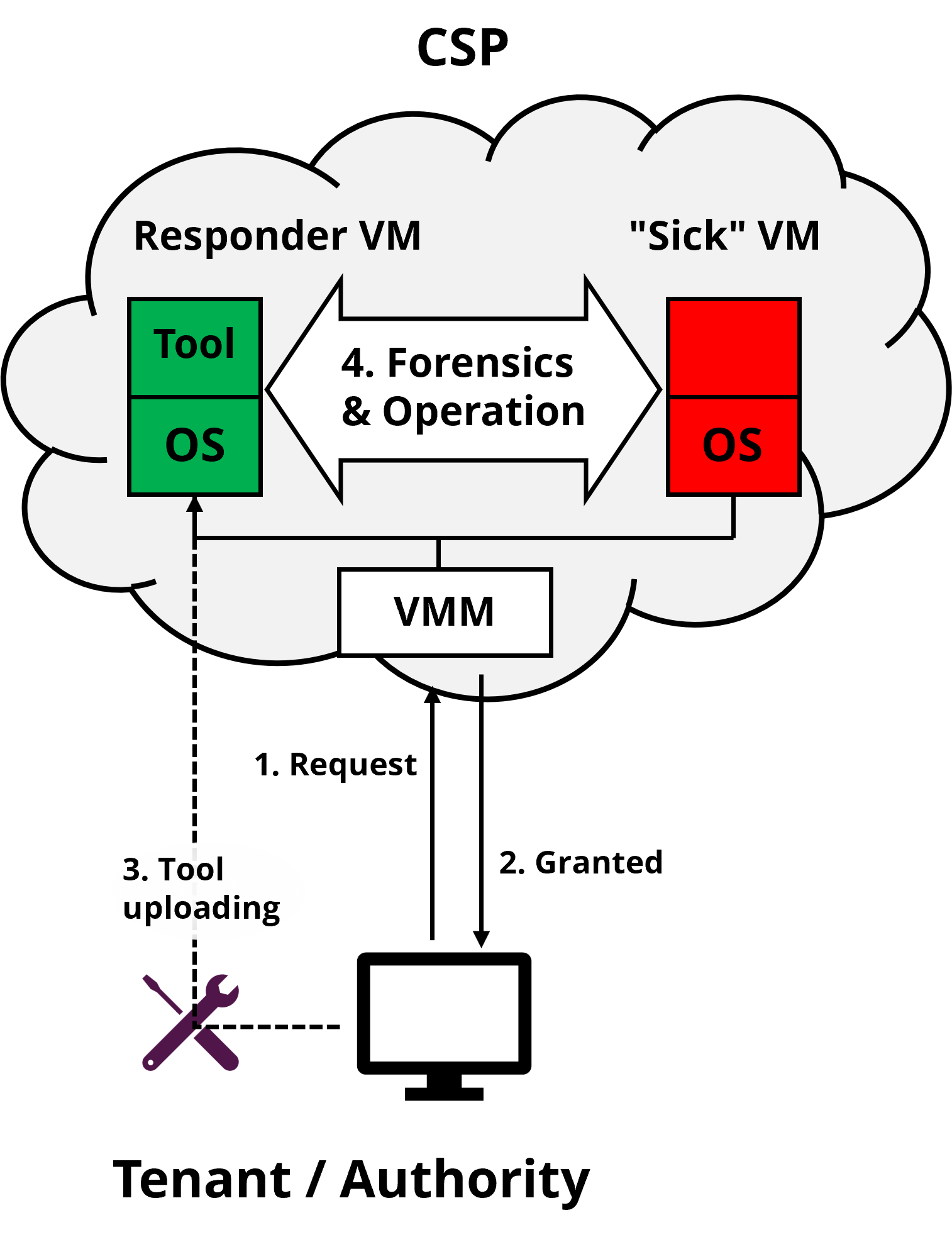
No remedy for misbehaving "sick" VMs due to errors or attacks.
Technical approach
- CSP provides an infrastructure for VMCare. (vm hospital)
- Tenant (or Authority) uses its own tool to introspect and/or rectify the live but misbehaving virtual machine. (vm surgeon)
Impact
- A new cloud service and business model benefit CSP, tenants and authorities.
- Extensible to Android phones to harden user interfaces and analyze malicious apps.
Translation opportunities
- Collaborate with ST Engineering and HTX to conduct pilot tests for feasibility evaluation.
- Apply translation fund to develop an operational prototype and market exploration.
Data breaches are a growing risk [IBM Cost of A Data Breach Report 2023]
- average cost of a data breach in 2023 was USD4.45m, a 15% increase over 3 years
- 82% of breaches involved data stored in the cloud
Limitations of existing cloud data security solutions
- access control is enforced by could service providers and can be by-passed due to backend misconfigurations and leakage of user credentials
- Extensible to Android phones to harden user interfaces and analyze malicious apps.
Technical approach
- access control policies are managed by user organizations and enforced by TEE
- seamlessly integrate TEE and E2E encryption to eliminate top attack vectors
- Support standard/prevalent access control mechanisms to maintain interoperability with popular could platforms
Translation opportunities
- Work closely with collaborators (DSTA, GovTech, HTX, ST EE) to meet users/market requirements
- Seek translational funding to develop an operational prototype and conduct extensive user trials
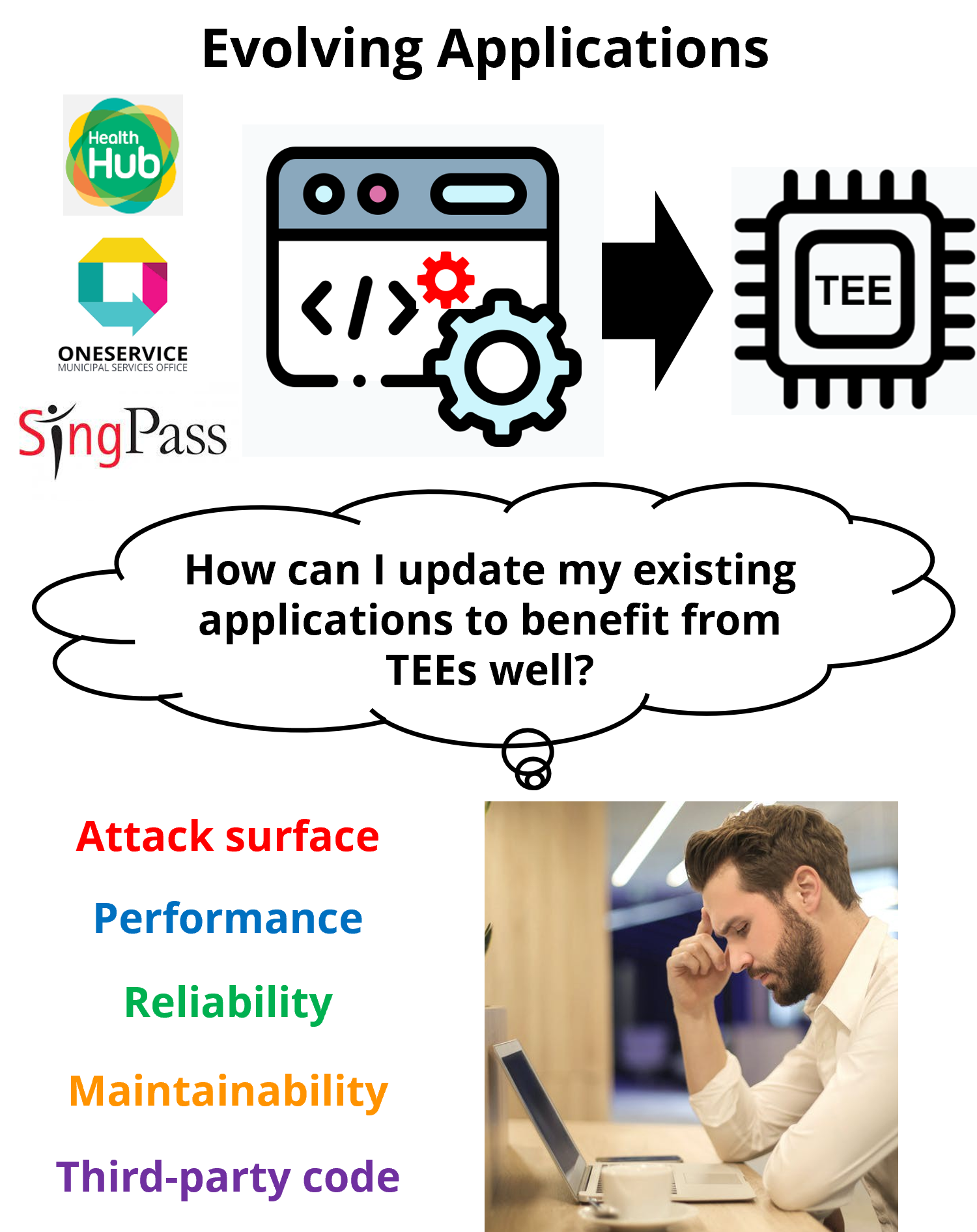
Why TEE?
Isolating sensitive code and data-in-use in TEE protects them from vulnerabilities in the rest of the app. The usage of TEE is recommended, e.g., in the Monetary Authority of Singapore’s advisory.Problem
- Many applications are not designed for or protected by TEE. Migrating and maintaining an evolving app to properly take advantage of TEEs is complex, time-consuming, and error-prone.
- Bad migration leads to little benefit and even harm.
Technical approach
- Realize a toolchain (Shield-It!, Forge-It!, and Fix-It!) for reengineering & maintenance of evolving applications to benefit from TEE while minimizing costs.
- Investigate SGX and the newly-released Android Virtualization Framework (AVF)
Translation opportunities
- App hardening service for government agencies and industry
- Collaborators: HTX, ST Engineering (project on SGX-protected credit card processing started)